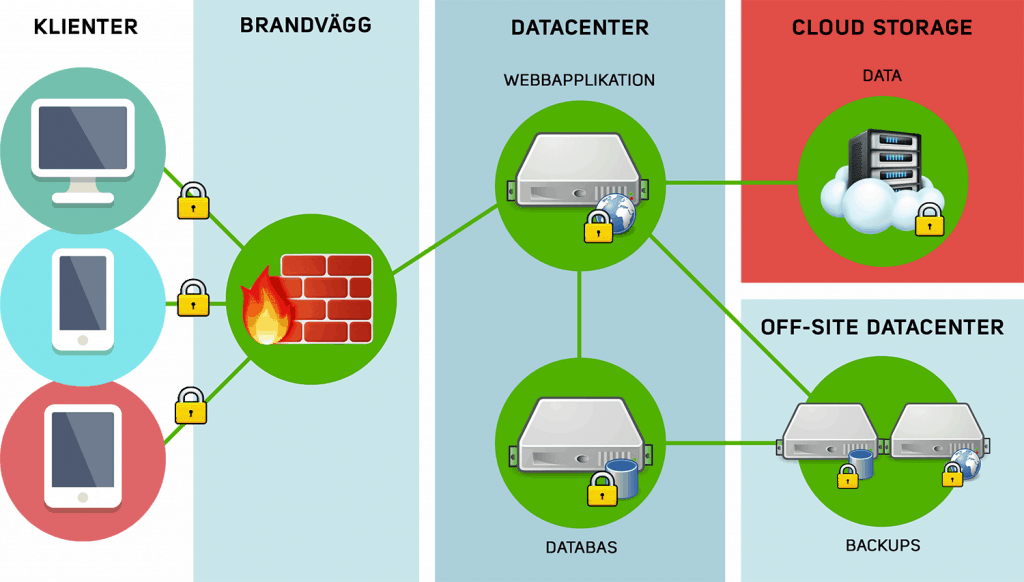
Recruto’s service is a so-called web service and is operated by Recruto’s partner for IT services, Glesys in Falkenberg. In Glesy’s infrastructure there are monitoring and alarm systems for handling any interruptions in Internet connection, power supply or cooling, as well as backup systems for those who take over to support operation during the interruptions. The Internet connection consists of several redundant core and distribution routers to protect against interruptions in the connection.
The IT environment on which Recruto operates is a Linux installation with a long life and support time, and as a base MySQL database with Apache and PHP. The system is automatically updated with new security patches as soon as they are released. The IT environment is scalable and can also be load balanced in different nodes in Sweden.
In addition to Glesy’s monitoring of the system, Recruto also has its own via the Pingdom service to monitor performance and any errors.
Recruto runs two separate and individually independent backup solutions for increased security in the event of data loss. Backup #1 runs daily on the entire file system and stores these files within Glesys infrastructure for 14 days in Sweden. Backup #2 is run daily on the files used by the system (candidate files, applications, database etc) and stores these for 30 days, also within the Glesys infrastructure.
All backups are encrypted and cannot be read by an external party. All data and backups are stored in Sweden.
All communication with Recruto takes place through encrypted connection. The web services and apps communicate over HTTPS and have SSL certificates with SHA-256 encryption. Our API also manages secure data through this certificate. All communication during server administration is through encrypted connection via SSH.
Recruto’s database is used to store the data needed to connect suitable candidates / people with the right employer and workplace. The users’ passwords in the database are encrypted, salted and initiated / hashed individually.
